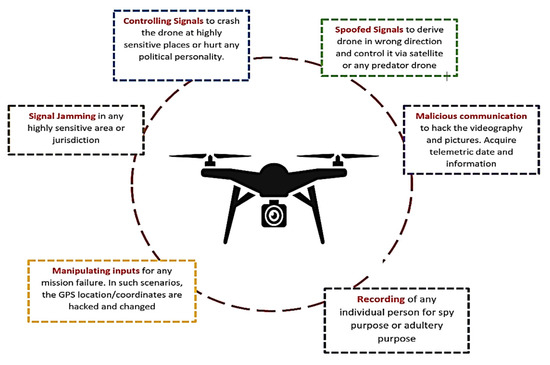
Drones | Free Full-Text | Comprehensive Review of UAV Detection, Security, and Communication Advancements to Prevent Threats
Public Health Preparedness Capabilities: National Standards for State and Local Planning | State and Local Readiness | CDC



:max_bytes(150000):strip_icc()/Enterprise-risk-management_final-3fb67ffdaafb4d3b879de7a0940f6fe7.png)